[Beginners guide to Deliverability] Lesson 4, Authentication and prevention
Lesson 4, Authentication and prevention
As discussed in Lesson 1, the history of email, Deliverability is forever developing, not only to suit how people are intereacting with email but also to try and prevent some of the attacks that threaten ESPs, ISPs and their consumers.
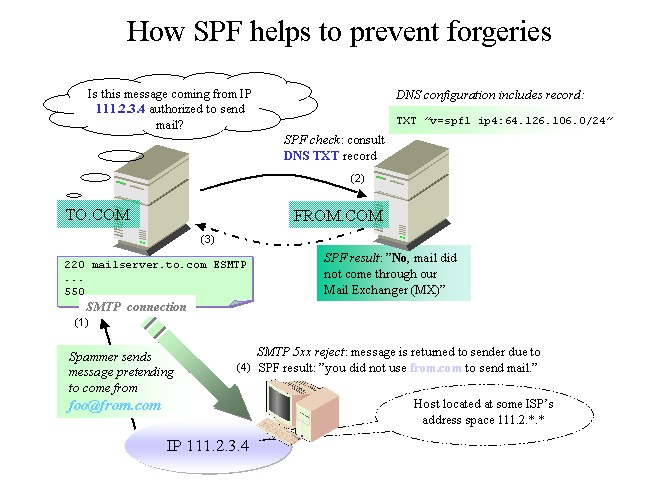
One of the burning questions with email is, how do we know this email is from who it says its from, how do we know if this is a legitimate email?
Luckily for us, there are ways in which we can obtain this information and this is vital for us to have confidence in the knowledge that our emails are authenticated.
There are several types of authentication, to name the most commonly known ones they are:
SPF
DKIM
Sender ID
DMARC
Below i shall briefly describe how they work to authenticate emails and prevent the attacks mentioned in Lesson 3.